Finding Password Reset Vulnerabilities
Learn how to identify and exploit common password reset vulnerabilities in web applications.
Read on MediumRead our Medium publications on cybersecurity topics
 Bug Bounty
Bug Bounty
Learn how to identify and exploit common password reset vulnerabilities in web applications.
Read on Medium Tooling
Tooling
Discover our powerful tool for testing Cross-Origin Resource Sharing configurations and vulnerabilities.
Read on Medium Bug Bounty
Bug Bounty
Proven strategies and techniques to maximize your success in bug bounty programs.
Read on Medium Vulnerability
Vulnerability
Technical analysis of an unauthenticated information disclosure vulnerability in Atlassian Jira.
Read on Medium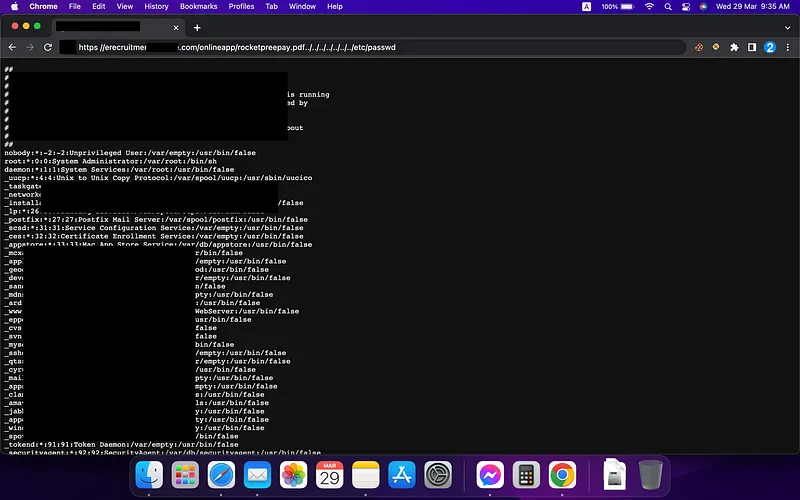 Exploit
Exploit
A case study of discovering and exploiting a Local File Inclusion vulnerability in a major network.
Read on Medium Bug Bounty
Bug Bounty
How I discovered and reported an open redirect vulnerability in Epic Games that earned my first bounty.
Read on Medium